Greetings, digital guardians. Today, we’ll be diving into the wonderful world of External Attack Surface Management (EASM) platforms. As the sun rises on another day in your cyber kingdom, you may find yourself wondering whether your EASM platform is really up to the task of protecting it.
In this article, we’ll be your guiding light in the dark alleys of EASM uncertainty. Together, we’ll explore the landscape of EASM solutions, uncovering the secrets of the strongest EASM providers who fortify your cyber defenses and ensure that your data remains unbreached. Prepare yourselves as we delve into the essential features that your EASM platform needs.
1. Enable developers to remedy vulnerabilities
Does your EASM platform empower your developers? If not, it’s time for an upgrade. The best EASM tools provide actionable information, helping your development teams and security teams join forces to vanquish vulnerabilities and achieve faster remediation times. It’s like having your own superhero duo!
Consider this: Your EASM platform should give your developers access to a centralized dashboard where they can see all vulnerabilities, their severity, and suggested remediation steps. This way, they can quickly and efficiently tackle security issues. Plus, integrating the EASM platform with your existing tools (like Jira or GitHub) can streamline the remediation process and make everyone’s life easier. (More on that later.)
Learn more about empowering your developers in the e-book Deep dive: How EASM is outpacing DAST for AppSec teams.
2. Provide continuous monitoring capabilities
Today, tech environments change too rapidly for organizations to keep up with them. Continuous monitoring is a must-have for any EASM platform to keep up with cloud systems, server settings, networks, and more. After all, you wouldn’t want to miss a thing, would you?
When considering the constantly evolving world of technology, it’s only reasonable to assume that a robust EASM platform should be able to adapt to and keep up with these changes. In other words, it should automatically update its threat intelligence database to detect new vulnerabilities and anomalies. With continuous monitoring, your organization can stay one step ahead of cybercriminals.
3. Combine automation with crowdsourcing
Have you ever dreamt of having an army of security experts at your disposal? EASM platforms that combine automated vulnerability scanning with crowdsourced security research are the answer to your dreams. Unleash the power of the crowd and enjoy unparalleled protection!

By integrating an EASM platform with the power of “the crowd”, you create a powerful synergy. The platform automates the scanning process, while the crowdsourcing incentivizes security researchers to upgrade the scanning capabilities. This combination helps ensure that your organization stays ahead of emerging threats.
4. Be easy to use
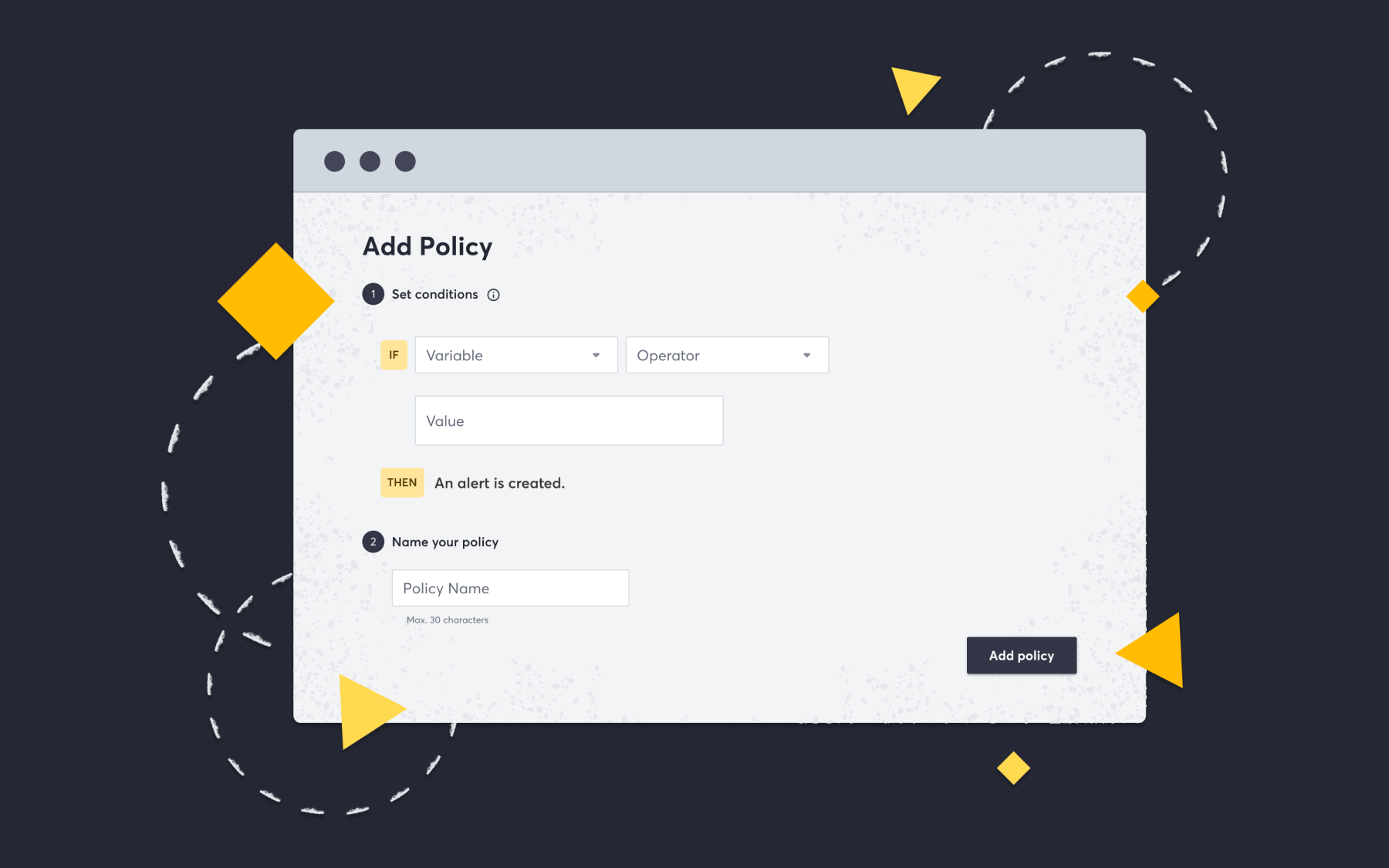
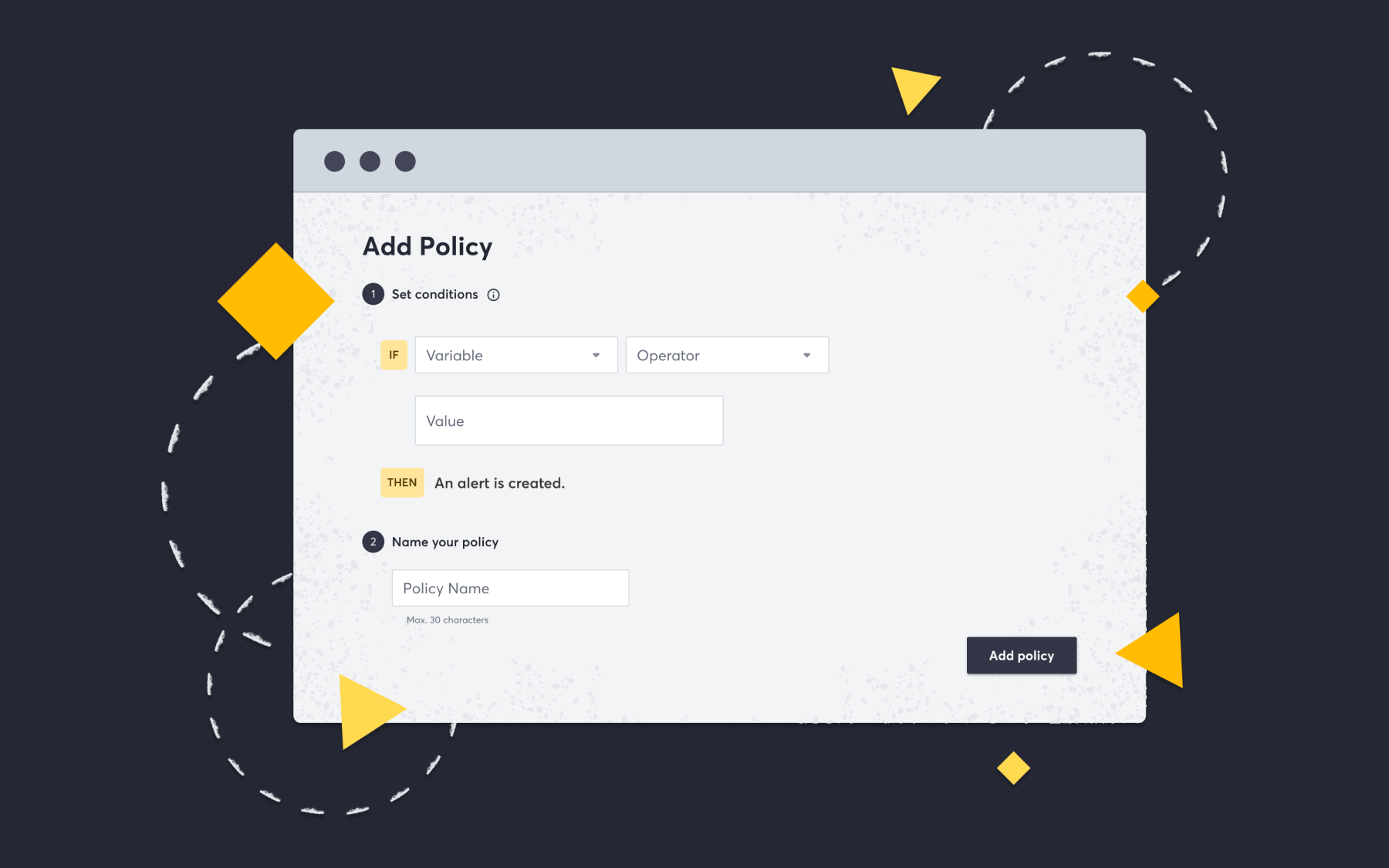
Who doesn’t love a user-friendly interface? Your EASM platform should make it a breeze to communicate vulnerability statuses to the right teams. Remember, it’s not just about the techies; business folks need to see those metrics too!
A great EASM platform will have customizable dashboards and reporting tools that cater to different audiences within your organization. From high-level executive summaries to detailed technical reports, your platform should make it easy for everyone to understand the current state of your organization’s security posture.
It’s also important that it’s simple and quick to perform EASM related tasks, such as adding a new asset, kicking off scans, and reviewing results. The easier the process is, the more likely it is to get done. The best part of EASM platforms that offer these capabilities is that these tasks are completely automated and scheduled, so they require little to no effort for teams to carry out and maintain.
5. Cover the entire attack surface
Is your EASM platform a master of reconnaissance? It should be. Make sure it covers every nook and cranny of your digital empire, from subdomains to exposed files. Continuous scanning is key to keeping your custom applications secure.
Most organizations have a larger attack surface than they realize. The good news? With cloud adoption on the rise, expanding an organization’s attack surface is only getting easier. Every system that comes online decreases the likelihood of vulnerability, and the increasing complexity of those systems does the same.
6. Work with existing systems
Nobody likes starting from scratch. Your EASM platform should play well with your existing systems and workflows. Why reinvent the wheel when you can just make it better?
Choose an EASM platform that offers seamless integration with your existing tools, such as issue trackers, SIEM, SOAR, or incident management solutions. Comprehensive EASM solutions should make the security team’s life easier, not just be another dashboard to check. Integration with your existing tooling will help you maximize the value of your existing security investments and ensure a smooth transition when implementing an EASM platform.
7. Find all (including unknown) assets
Last but not least, your EASM platform should have a Sherlock Holmes-level knack for discovering assets. With the ever-changing landscape of modern enterprises, keeping track of new assets can be a Herculean task. Your platform should be up to the challenge!
Finding unknown assets requires a combination of different reconnaissance techniques, including (but not limited to) utilizing third-party APIs, scouring certificate transparency logs, parsing ASN data, DNS brute forcing, and more.
The ideal EASM platform will automatically discover and inventory all your assets, including those you didn’t even know existed. This comprehensive asset visibility allows you to identify and address vulnerabilities across your entire attack surface, leaving no stone unturned.
Try Detectify’s EASM platform
There you have it, folks: We’ve walked through seven essential features that your EASM platform should boast for optimal performance and utility for your organization. So, what are you waiting for? It’s time to go forth and conquer your digital domain with confidence.
And remember, if your EASM platform isn’t up to snuff, it might be time for a change. Book a demo of Detectify’s complete standalone EASM platform to learn how you can start covering your external attack surface with rigorous discovery, 99.7% accurate vulnerability assessments, and accelerated remediation through actionable guidance.