
The 29-minute Breakout: Why monthly vulnerability scanning no longer works
TLDR: We attended Cyber Security 2026: Kritisk infrastruktur in Stockholm, and the reality check was simple: “breakout time” has hit a record low of 29 …
Ryan Rudder
Gone are the days when gate-based security processes were the most effective way to ensure security of an organization’s external attack surface. Getting the security team to sign off on every new application or asset before they go live simply is not scalable.
One of the most prevalent realizations in the cybersecurity world over the last 5 years has been that many organizations are simply not aware of the vastness of their external attack surface. This has given rise to a defensive principle called “External Attack Surface Management“, or EASM. Without an EASM program at your organization, there is a high chance that your external assets will fall into a state of vulnerability at some point. In this article, we’ll discuss why this is the case and how we might defend against it.
EASM involves the monitoring of all external entry points that could be used to gain access to systems to extract sensitive information or data. EASM aims to address many of the security challenges that come with our fast-paced ways of doing business, including the rapid adoption of cloud-based technologies and infrastructure, as well as the digital transformation projects many companies are managing. Keeping track of the shifting landscape of assets is where a strong EASM program really shines and becomes a key tool for security teams.
Assets now encompass practically any internet-facing system that stores, transmits, or has access to company data. This can include mobile devices, web applications, cloud infrastructure, third-party services, and shadow IT services and devices, amongst many others. Both attackers and hackers are actively scanning the internet for vulnerable assets constantly.
The question for your company is no longer, “Should we be doing EASM?” but, “How can we do EASM?” EASM can become another tool in your company’s arsenal keeping sensitive information and data safe. The key is to start implementing a program now, no matter how small it begins, and keep iterating upon it.
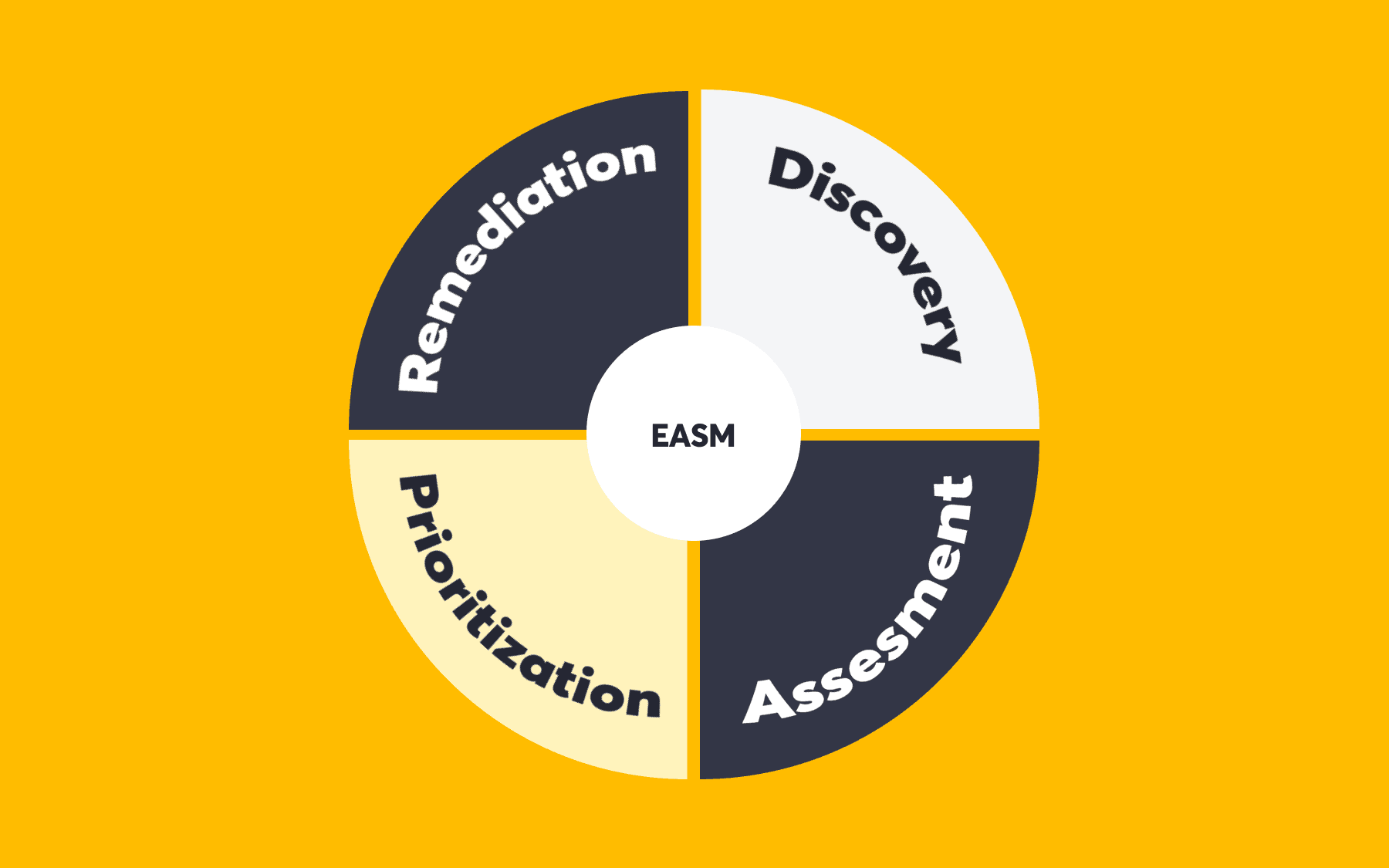
An EASM program can be broken down into four phases:
This phase focuses on mapping out all of your company’s assets and identifying what your attack surface looks like. Often referred to as reconnaissance, or performing OSINT, this discovery phase often involves identifying DNS records, SSL certificates, cloud-based systems, applications, APIs, subdomains, and IP addresses, amongst other things.
Tip! Things to keep in mind: What shadow IT has been implemented without your knowledge? Good discovery also encompasses checks for company data on social platforms, as well as places like GitHub where teams may be leaking data or credentials.
It’s imperative to know whether your externally facing assets and endpoints are exploitable or associated with a known risk. This phase can be a lot of effort for a single security team to handle, that’s where a dedicated group of ethical hackers can ensure continuous, full breadth and depth coverage and reduction in false positives and false negatives.
Tip! This is a complex phase with a lot of moving parts. Group vulnerability types together and break down this phase into smaller chunks depending on the third-party applications you use.
Once you’ve got a list of assets and known vulnerabilities, what do you do with it all? Before you dive into action fixing things, it’s important to classify and categorize the risk associated with your exposed assets, as not everything will be a critical risk to your business. This phase helps you know where to focus your efforts and attention first, and what the next best steps are in addressing potential risks at all times. An internal risk assessment can be based on any risk framework but the CVSS framework is a good place to start if you’re undecided.
Tip! Risk categorization is hard work, but keep in mind that the effort provided upfront in this phase will greatly assist future phases and make new iterations of your EASM program smoother.
This is where you get to take action and can see measurable results, whether that be a reduction in attack surface by the removal of unused assets from the internet or the closing out of a vulnerability. What gives your security team an advantage here is actually the work done upfront in the previous 3 phases to identify, assess and categorize external facing assets. The speed and accuracy of these steps means faster remediation times and less exposure of your company’s data to the internet.
Tip! Process workflows don’t stop when they get to this phase. Ensure that your security team is set up for success so that they know exactly what to do with each vulnerability and are empowered to address each risk.
Imbalance between tech tools and human talent
While it’s important to get the right tools in place to make the ASM program successful, you need to bring people along for the journey which includes both – the security team implementing the EASM solution as well as the employees of that organization. For the teams that will be managing and contributing to the EASM program in their day-to-day work, integrate it as a part of their existing workflows and systems. For the C-Suite and executives, it’s important to convey how the EASM program reduces overall risk to the business and elevates the success of many teams.
Don’t forget to explain why this program is important in helping uplift the security of the whole company and how the tiny changes that they make to their daily workflows contribute to its success. Empower your people to speak up and feel confident about security.
There is no magic pill to implementing an effective EASM program. Start small and iterate upon it. Have a blend of open-source software, in-house and third-party tools for your EASM program that complement each other. This will help you lean on the strength of your internal teams who will be maintaining this program without burning them out.
From here, the key is to ensure that this process is repeatable for your company. The more you can iterate upon scanning and compare data from each subsequent workflow through phases, the better. Don’t forget to regularly review the process and tweak it to your business needs and workflows. It’s also important to do some assurance checks on the EASM program to validate that the system is capturing, analyzing, and remediating all of your attack surface.
Once an EASM program is established it can be used to uplift other security tools and teams, such as traditional vulnerability management programs, application development, as well as the capabilities of the security operations center, threat intelligence, and red teams. Detectify offers both surface monitoring and application scanning so you can get the breadth and depth of coverage that your company needs. Get in touch with us to see how we can help your company be proactive in fixing vulnerabilities across your company’s entire IT ecosystem.

TLDR: We attended Cyber Security 2026: Kritisk infrastruktur in Stockholm, and the reality check was simple: “breakout time” has hit a record low of 29 …

Detectify vs Acunetix is a common comparison for AppSec teams evaluating Dynamic Application Security Testing (DAST) tools. This article provides a direct comparison between Detectify …