TL/DR: Detectify is aiming to make security understandable and easy to work with. That is why we visualize your security status in several ways in the tool: You can track the progress over time and your Threat Score gives you an instant security level ranking. In the blog post, we will focus on how you should interpret and work with your Threat Score.
Where do you find your threat score?
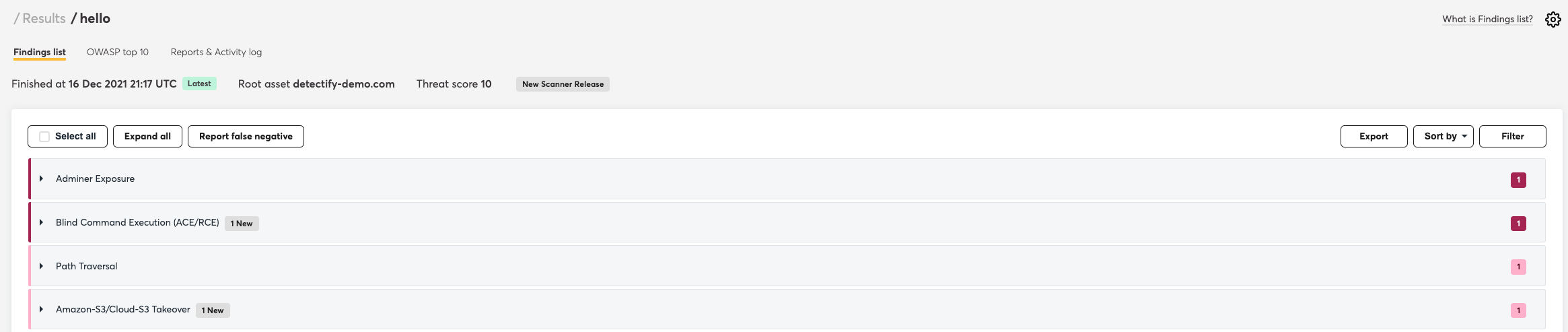
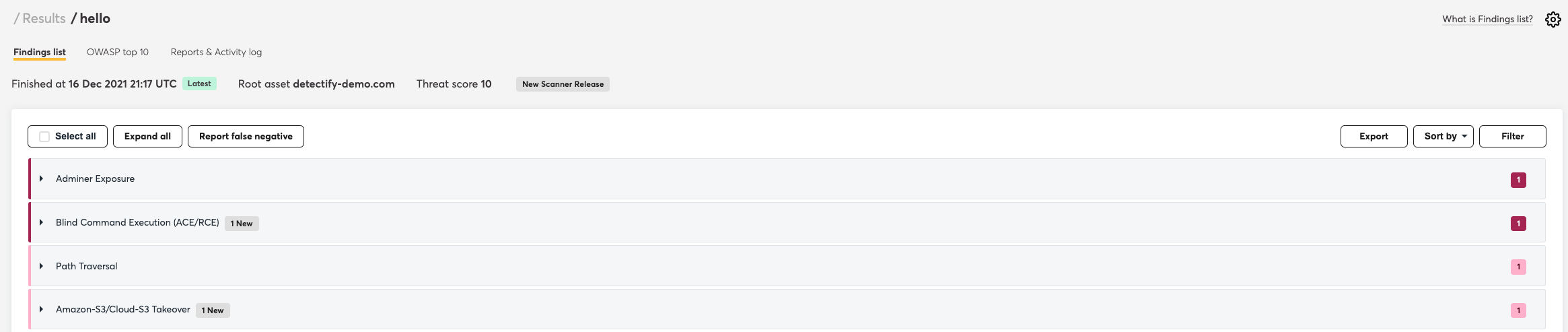
Pick which Scan Profile you want to find out the score for. The threat score is visible in the top right (highlighted in the example below). As you can see, the score is dynamic and varies from scan to scan – it all depends on if you have fixed previous vulnerabilities, or if we’ve added new security issues to the scanner.
What is the score based on?
The vulnerabilities’ severity level (that we use to calculate the end result) is based on CVSS version 3.1 which focuses on ironing out the meaning of various attack vectors. Different factors and configurations may allow for the same vulnerability to have multiple, different base scores depending on the context. This is useful when a vulnerability on a particular system configuration or operating system may not pose a high severity, but it would on another.
The new CVSS version also accounts for concepts such as vulnerability chaining. This is when an attacker follows steps to carry out a series of attacks after performing some basic reconnaissance.
Key differences between v2 and v3
The most prominent change that CVSS v3.1 brings is that it measures severity, not risk. It also adds the critical severity level. This level applies to vulnerabilities scored 9-10. In the words of The CVSS v3.1 User Guide: “The CVSS Specification Document has been updated to emphasize and clarify the fact that CVSS is designed to measure the severity of a vulnerability and should not be used alone to assess risk.”
The new version aims to address and correct a common mistake where the CVSS Base Score was seen as the only factor for assessing risk, rather than a comprehensive risk assessment system. The main changes in v3.1 clarify the definitions of base metrics such as Attack Vector, Scope, Privileges Required, Security Requirements and more definitions.
In order to ensure a consistent scoring standard across all industries, changes to the CVSS v3.1 include clarification of the definitions and explanation of existing base metrics, an expanded and refined version of the CVSS Glossary of Terms as well as the CVSS Extensions Framework. This is a new standard method of extending CVSS that allows a scoring provider to include additional metrics and metric groups while retaining the official Base, Temporal, and Environmental Metrics.
For instance, previously a vulnerability with a low base score would normally have been ignored under the impression it poses a low risk. But CVSS 3.1 takes into account specific circumstances such as the network architecture and overall configuration. Consequently, a vulnerability that previously scored ‘low’ may be highly exploitable when it comes to the network design of your company.
Advantages of using CVSS v3.1
While the change in CVSS scoring may seem minimal and cumbersome, CVSS v3.1 can have a big impact. It provides users with a more comprehensive and precise context and shared understanding. The updated standard affects not only the CVSS score but also the way we assess our risk and address security vulnerabilities.
How do I interpret my score?
You already know that we categorize vulnerabilities as High, Medium or Low severity findings in order to make it easier for you to prioritize your security work. As we described earlier, it is the severity level of the vulnerabilities identified on your site that is the basis of your Threat Score.
My score is: 0.1-3.9
Remember that several Low severity vulnerabilities can still compromise your security
If your score is on the lower part of the scale, it means you have Low severity vulnerabilities on your site. These vulnerabilities might not individually constitute a critical risk, but we want to emphasize that even though your score is relatively low, this does not mean you are not at risk. Low findings may not individually compromise your security, but in combination with each other, they can be used for more advanced attacks.
My score is: 4.0-6.9
You have Medium severity findings to take care of
If your score is between 4.0-6.9, you most likely have several Medium severity vulnerabilities on your site. About 90% of our users have Medium vulnerabilities, so you are not alone. As mentioned earlier, when these vulnerabilities are combined with each other, they can pose a very high risk, so we recommend you to fix them as soon as possible.
My score is: 7.0-8.9
Ouch, you have some serious security work to do.
A score between 7.0-8.9 means you have one or more crucial security issues to take care of immediately. About 30% of our users have high severity findings in their reports. If the Detectify scanner identifies one or more High severity findings on your site, these will automatically pull you up its specific CVSS score, since these vulnerabilities individually represent such a high risk.
My score is: 9.0-10.0
Critical vulnerabilities found. Danger zone.
Vulnerabilities that score in the critical range usually mean that the exploitation of the vulnerability results in root-level compromise of servers or infrastructure devices. For critical vulnerabilities, is advised that you patch or upgrade as soon as possible unless you have other mitigating measures in place.
The easiest way to lower your score is to solve all High and Critical severity vulnerabilities as soon as possible.
Difference between CVSS and CVE
CVE stands for Common Vulnerability Enumeration, which is a unique identifier for each vulnerability listed in the NIST NVD. CVSS provides an indication of the severity of each CVE.
The CVE format is: CVE-[4 Digit Year]-[Sequential Identifier]
If you have any questions about the score, or need any help validating your findings, send us a note on hello@detectify.com and we be more than happy to help you.
To become a real Detectify Pro-user, we also recommend you to read the following articles:
– Setting up your account the right way
– 5 things we’ve done to make your Detectify experience better
Happy scanning!
// The Detectify Team